
DORA compliance for file sharing, access and collaboration necessitates the implementation of Zero Trust Data Access (ZTDA). ZTDA has stringent security measures such as granular access control, continuous authentication, encryption, micro-segmentation, and activity monitoring that align with the Digital Operational Resilience Act’s rigorous standards for cybersecurity and operational resilience within the financial sector.
DORA Compliance for File Sharing, Access and Collaboration Using Zero Trust Data Access
Estimated reading time: 6 minutes
Table of Contents
-
- What is DORA?
- What are the DORA Requirements for User Access, Sharing and Collaboration?
- Using Zero Trust Data Access for DORA Compliance
- Why a Zero Trust Architecture Matters for DORA Compliance
- How Zero Trust Data Access Contributes to DORA Compliance
- Use Cases for Zero Trust Data Access in the DORA-Compliant Financial Institution
- Summary – Zero Trust Data Access Crucial for DORA Compliance in Financial Sector Security
What is DORA?
What are the DORA Requirements for User Access, Sharing and Collaboration of Unstructured Data?
Regarding user access, sharing, and collaboration of files and folders, it’s expected that financial entities falling under DORA’s scope would need to adhere to broader cybersecurity and operational resilience principles. This includes implementing robust access controls, secure sharing protocols, encrypted communication channels, and ensuring collaboration tools meet security standards.
Some of the compliance requirements for user access, sharing and collaboration with DORA are:
Access Control:
- Financial entities and ICT providers must implement appropriate policies and procedures to manage the access rights and permissions of their users, including authentication, authorization, revocation, and auditing.
User Education:
- Financial entities and ICT providers must ensure that their users are aware of their roles and responsibilities regarding the use and protection of ICT systems and data and provide them with adequate training and awareness programs.
Secure Sharing and Collaboration:
- Financial entities and ICT providers must enable secure and efficient sharing and collaboration of data and information among their users, as well as with external parties, such as regulators, auditors, or customers.
Monitoring and Incident Reporting:
- Financial entities and ICT providers must monitor and report any incidents or anomalies affecting the availability, integrity, or confidentiality of their ICT systems and data, and take appropriate measures to contain, mitigate, and recover from them.
Using Zero Trust Data Access for DORA Compliance for Unstructured Data
Zero Trust Data Access (ZTDA) emerges as a valuable tool for financial organizations striving for DORA compliance, particularly in handling unstructured data (documents and files) within intra or inter-company communications. (It is not a solution for structured data such as individual financial transactions involving money, records, or specific pieces of data.)
In the exchange of financial and non-financial documents, ZTDA aligns with common industry practices to ensure a tailored security strategy for unstructured data and effectively addresses the unique security requirements of DORA, thereby enhancing overall compliance efforts while mitigating potential risks.
Implementing a Zero Trust Data Access can significantly aid in meeting compliance requirements outlined in the Digital Operational Resilience Act (DORA) by enhancing the security and resilience of financial entities’ IT systems and operations. Zero Trust is a cybersecurity model centered on the principle of not automatically trusting any user or device inside or outside a network. Users must be verified and specific access requests must be authorized before granting access. This is achieved via a zero trust architecture – see What is Zero Trust Data Access (ZTDA)?
Why a Zero Trust Architecture Matters for DORA Compliance
Implementing a Zero Trust Architecture (ZTA) is crucial for meeting DORA (Department of Regulatory Agencies) compliance standards. This architectural framework aligns closely with the principles outlined in NIST SP-800-171v2, specifically emphasizing zero trust access control. (See How to Meet NIST Guidelines for Zero Trust for Remote Data Access.)
Within this framework, a central server plays a critical role in verifying user identities and permissions. Instead of allowing direct shared access to the original resource location, the server facilitates the delivery of requested files to users. This approach is visualized in Diagram 1, illustrating a simplified zero-trust architecture.
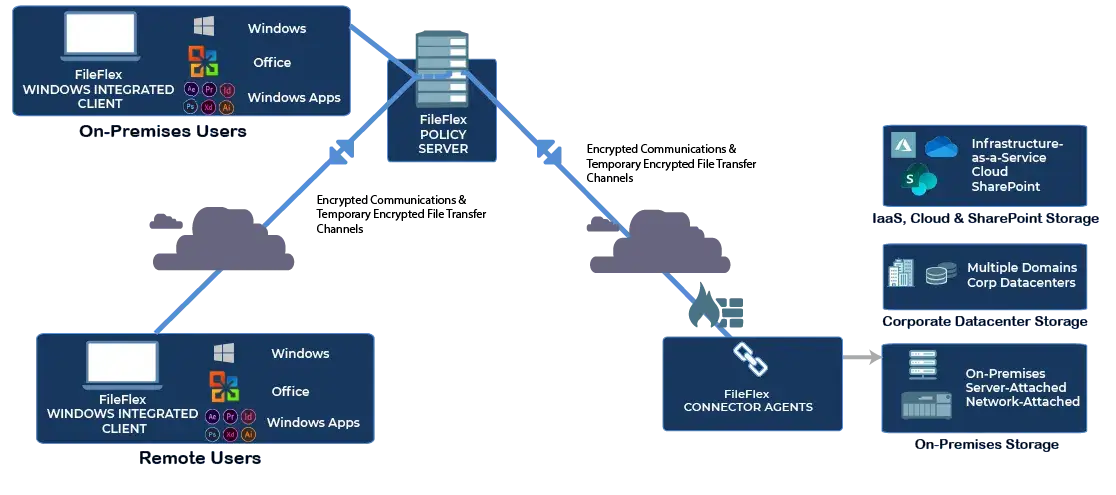 Diagram 1
Diagram 1
Simplified Zero Trust Architecture for DORA Compliance
This method enables seamless access, sharing, collaboration, and management of files and folders across various repositories—be it cloud-based, FTP, SharePoint, or on-premises storage. Notably, there’s no need for the zero trust policy server to be managed by a third party, and sensitive information remains secure without requiring uploads to an external server.
Management retains detailed control over access and restrictions, aligning with the principle of Least Privilege and the established IT hierarchy. Additionally, by centralizing all actions through the zero-trust server, comprehensive records of activities are maintained, aiding forensic investigations and for output to the SIEM to detect ransomware attacks in progress (see How to Reduce Ransomware Risk Using Zero Trust Data Access).
Implementing zero trust principles via a ZTA is the key to achieving DORA compliance regarding secure access, sharing, and collaboration.
How Zero Trust Data Access Contributes to DORA Compliance
Here’s how Zero Trust Data Access as implemented by FileFlex Enterprise can contribute to DORA compliance:
Granular Access Control:
- Zero Trust Data Access emphasizes the principle of least privilege, ensuring that users only have access to the specific resources they need for their roles. This approach helps financial entities manage user access more effectively, reducing the risk of unauthorized access to sensitive data or critical systems, which aligns with the security requirements of DORA.
Continuous Authentication and Authorization:
- Zero Trust Data Access continuously verifies and authenticates users and devices before granting access to resources. By implementing strong authentication mechanisms and constantly monitoring and validating access attempts, financial entities can enhance their security posture, meeting DORA’s requirements for robust authentication and access controls.
Encryption and Data Protection:
- Zero Trust Data Access incorporates encryption, double encryption (encrypted data in an encrypted micro-channel), and other data-centric security measures. By encrypting data-in-motion and ensuring that access controls are applied consistently across all data interactions, financial firms can better protect information and align with DORA’s objectives for data security and resilience.
Microsegmentation:
- Zero Trust Data Access (ZTDA) focuses on securing access to individual files and folders as the smallest implicit trust zone. By isolating different network access to the file and folder level, organizations can restrict the lateral movement of threats to reduce the threat surface and help prevent them from spreading across the entire network. This strategy helps contain potential breaches and limits the impact of cyber incidents, aligning with DORA’s goals for minimizing disruptions and improving operational resilience. (See Why You Need Zero Trust Data Access Micro-Segmentation.)
Activity Monitoring:
- Since all actions must be authenticated and authorized by the zero trust policy server, ZTDA provides detailed activity logs for data access and sharing, enabling IT managers to monitor user behavior, detect anomalies, and identify potential security threats. This enables prompt incident response and adherence to DORA’s requirements for incident reporting and response.
Use Cases for Zero Trust Data Access in the DORA-Compliant Financial Institution
Implementing a Zero Trust Data Access as implemented by FileFlex Enterprise aligns with the core principles of cybersecurity, access control, and risk management that are central to DORA compliance. Adopting this approach can significantly enhance the operational resilience and security posture of financial entities, ultimately helping them meet the spirit and intent of DORA’s requirements for unstructured data. Some practical use cases for the implementation of Zero Trust Data Access as implemented by FileFlex Enterprise are as follows:
DORA Compliant VPN Alternative
ZTDA can be used as a DORA-compliant VPN alternative that delivers cutting-edge security, simplified access management, IT-controlled chain of command, file sharing/collaboration functionality, and with Windows integration, enhanced user experience. See 19 Advantages of the Zero Trust Data Access VPN Alternative.
DORA Compliant Secure File Sharing
ZTDA provides DORA-compliant file-sharing that delivers data protection, efficient sharing of federated storage, simplifies the user experience, enhances data privacy and compliance, provides exemplary data governance and an IT-controlled chain of command with no duplication or syncing. See Zero Trust Data Access for Secure File-Sharing.
DORA Compliant FTP Alternative
ZTDA is a DORA-compliant FTP alternative that offers cutting-edge security, ransomware prevention, regulatory compliance, simplified management, enhanced user experience, and more. Read Zero Trust Data Access as an FTP Alternative
DORA Compliant MFT Alternative
ZTDA is a contemporary alternative that addresses the security vulnerabilities of MFT. It offers granular file and folder micro-segmentation, has unique federated storage management, encompasses distinctive granular contractor access and brings an IT-controlled chain of command. For more see, Zero Trust Data Access as a Managed File Transfer Alternative.
DORA Compliant Zero Trust Content Collaboration
ZTDA can be used as a DORA-compliant zero trust content collaboration platform that safeguards data through micro-segmentation and stringent access to elevate security, streamline workflows, reduce the risk of ransomware and more, providing a cost-effective, adaptable, and user-friendly solution. See Content Collaboration Using Zero Trust Data Access.
DORA Compliant Virtual Data Rooms
Delivers DORA-compliant Zero Trust Virtual Data Rooms that offer superior data security, robust protection against ransomware, superior governance and chain-of-command and comprehensive insider threat prevention, while also ensuring compliance, reducing the attack surface, and providing a cost-effective, future-proof approach. Read Top 13 Reasons to Adopt Zero Trust Secure Virtual Data Rooms.
DORA Compliant Enhancement for Microsoft 365
Integrating into Microsoft 365 E5, particularly for remote and external users, elevates security posture, reduces the risk of data breaches, enhances regulatory compliance, and mitigates insider threats, ultimately fortifying data protection and access management within the Microsoft ecosystem. See 21 Reasons to Supplement Microsoft 365 E5 Security with Zero Trust Data Access.
DORA Compliant SharePoint Add-in
As a SharePoint add-in, it delivers robust security, flexible data access, and compliance capabilities, making it indispensable for modern organizations prioritizing data protection and efficient collaboration, particularly for remote and external users. See 19 Reasons Why Zero Trust Data Access is an Essential SharePoint Add-in.
Reduces Your Costs
Zero Trust Data Access technology as implemented by FileFlex reduces your VPN, FTP, MFT, file sharing, content collaboration, virtual data room and cloud storage setup, maintenance and use to dramatically reduce your costs. See How Zero Trust Data Access Cuts Costs in Organizational Operations.
Summary – Zero Trust Data Access Crucial for DORA Compliance in Financial Sector Security
In conclusion, the integration of Zero Trust Data Access (ZTDA) as implemented by FileFlex Enterprise within financial entities is pivotal for meeting the stringent cybersecurity and operational resilience standards outlined in the Digital Operational Resilience Act (DORA), ensuring granular access control, continuous authentication, encryption, micro-segmentation, and activity monitoring, thus fortifying secure file sharing, access, and collaboration practices in line with DORA’s stringent mandates for the financial sector.
For further reading also see Critical Infrastructure Regulatory Compliance via Zero Trust Architectures and GDPR Compliant File Sharing Using Zero Trust Data Access.
Learn More About FileFlex Sign Up for a Free Trial