Frequently Asked Questions
All FAQs
-
Why Use FileFlex?
Some NAS manufacturers already have software that allows users to access, share and stream files stored on the NAS to remote devices. Unfortunately, however, that is where your device manufacturer’s software ends. It virtualizes access to the NAS, but nothing else. When you virtualize your NAS with FileFlex, you are also virtualizing access to all the devices and storage that are attached to the same network. You are virtualizing access to your server, any server attached storage such as a SAN, DAS, private cloud, or other NAS, and every PC and laptop on the same network. A NAS with FileFlex becomes a powerful gateway into all of it. With FileFlex on your NAS, you can use that NAS to access, share, stream and perform remote multi-device file management functions to any and all your storage on your network.
Watch the demo here to understand this better.
Sure you can subscribe to a cloud music streaming service, however, cloud music can’t match listening to your own personal music collection on your smart phone.
You Want To Stream From Your Own Storage
Building and maintaining a media collection is most convenient on your own PC or NAS (Network Attached Storage) device. That’s particularly true if you have a mix of MP3 backups from your CDs, digital downloads, and MP4 files from your video camera. Once organized neatly, you want to access, stream, or share them as easily as possible from all your devices – smart phone, tablet, or other computers.
The easiest way to take your entire media library with you, no matter where you go or what device you are using, is FileFlex. FileFlex virtualizes your storage so that you can access, share, and stream it from any smart phone, tablet, or computer.
Sure, you can upload your personal media files to the cloud and then stream them to your phone, and it is great in theory, but in real life, it just doesn’t stick. The upload process is slow and a hassle, and do you really want your personal stuff stored on someone else’s computer? We may start off this way with good intentions, but sooner or later the method breaks down.
You Want To Stream From Your Own Storage
Building and maintaining a media collection is most convenient on your own PC or NAS (Network Attached Storage) device. That’s particularly true if you have a mix of MP3 backups from your CDs, digital downloads and MP4 files from your video camera. Once organized neatly, you want to access, stream or share them as easily as possible from all your devices – smart phone, tablet or other computer.
The easiest way to take your entire media library with you no matter where you go or what device you're using is with FileFlex. FileFlex virtualizes your own storage so that you can access, share, and stream your media files from their source locations. You don’t need to upload them to third parties.
In short, yes – FileFlex is arguably the world’s best file manager app for remote file management between multiple devices. Normally, if you want to create a folder, rename a file, or cut, copy, and paste for example, your file manager will only you perform file management functions to storage that is either on your device or networked to your device. It works for devices you are connected to, but not when you are remote. However, in today’s age, the traditional file manager app has simply not kept up with the demands of users that work remotely using multiple devices from anywhere in the world. This is where the powerful file access virtualization technology of FileFlex kicks in. FileFlex allows for file management across all your storage – not just the storage on your device or networked to your device. You can be remote.
FileFlex virtualizes access to your files and folders no matter where they are on your storage infrastructure. They could be on your local drive or they could be on a network drive, they could be on the server of a remote office or they could be on your corporate cloud. It doesn’t matter. With FileFlex, you can access your stuff no matter where it is stored. Not just access, but you can manage all your files and folders remotely no matter where they are stored. That means that even when you are working remotely, you can navigate and organize. You can cut, copy, paste, upload, move, delete, and rename your stuff from a smart phone, tablet or secondary computer, even when you are away. You don’t have to be in the office to organize your network drives; you can keep things organized from anywhere.
FileFlex doesn’t stop there. It turns networked devices into a powerful gateway into all storage. For example, with FileFlex on a server (or NAS, router or networked PC), you can use that server to access, share, stream and perform remote multi-device file management functions to any and all the storage on the server and all storage on the server’s network. You are virtualizing access to the server, any server attached storage such as a NAS, SAN, DAS, private cloud and every PC and laptop on the same network as the server.
FileFlex organizes all your storage from a single dashboard and all of your storage is displayed with the same hierarchical navigational file manager no matter what device your files are stored on. It allows you to remotely manage files on and between any of your storage drives.
There are 2 versions of FileFlex. FileFlex and FileFlex Enterprise. FileFlex is designed for individuals and small business. With FileFlex, the user is in control of their FileFlex account. For example, you may want to share your music collection, movies, videos, files and documents with your friends or co-workers and let them access these files remotely from their source locations.
FileFlex Enterprise, on the other hand, is designed for organizations. With FileFlex Enterprise IT is in control of its organization's and its users' accounts. Using FileFlex Enterprise, the administrator sets which user, within a company, is allotted to what department, which storage repositories a user can access and what permissions a user has. FileFlex Enterprise allows an administrator to audit the company's and its user's activities.
Additionally, FileFlex Enterprise provides users with the ability to collaborate with each other using the collaboration tools. These tools lets users not only share a file, but also provides the option of letting the other user, with whom the file is being shared, download and edit their files.
Further, one of the most important features of FileFlex Enterprise is that the FileFlex Enterprise server is hosted either by the organization or the organization's Managed Service Provider. This allows the organization to keep governance, risk management and compliance (GRC) under their own GRC framework and under the control and policies of their IT department. With FileFlex Enterprise an organization does not have to share GRC with third-parties, reducing compliance headaches and simplifying the storage infrastructure. With FileFlex Enterprise, the organization itself manages a smaller environment, rather than a large and complex one shared with third parties. Overall, this translates to better control and a lower risk posture.
FileFlex Enterprise is a zero trust data access application that provides remote access and sharing to the entire company-owned storage infrastructure and puts it under IT control.
The product is available at www.fileflex.com. The Android client is available on the Google Play Store and the iOS client is available on the Apple App Store.
Remote Access – It provides you remote access to your files and folders no matter where you stored them. Access can be from a Windows, Mac, or Linux computer; Android, iOS, BlackBerry, or Windows tablet or smart phone; or any internet connected kiosk. The access to all storage is from a simple dashboard.
File Sharing – It allows you to remotely share files from their source locations without having to sync files to secondary locations. It does not use links that can be forwarded or copied to social media. Instead, it is permission-based to prevent unauthorized access. The files and folders you share act like an extension of your recipient’s local device. There are no storage limitations, no file size limits, no quality degradation (no compression), and no complicated IT type setup requirements for the sharing of files.
Media Streaming – It allows the streaming of media files from their source locations to the user or to any contact. This allows the consumption and sharing of massive collections of home videos, movies, and music by family and friends without any need to download the files.
Remote Multi-Location File Management – FileFlex is arguably the world’s best file manager app because it provides remote file management between multiple devices. The traditional file manager include an ability to create folders as well as cut, copy, paste, move, upload, and delete files. But that is where a traditional file manager ends. It works for devices you are connected to, but not when you are remote.
FileFlex enables you to use any internet connected smart phone, tablet or secondary computer to remotely cut, paste, copy, delete, rename, move, and organize any document no matter where it is stored. You can even cut, copy and paste files between your various storage devices remotely. You don’t have to be at home or in the office to organize your files; you can keep things organized from anywhere.
Remote Network Access – It turns networked devices into a powerful gateway into all storage. For example, with FileFlex on your server (or NAS, or networked PC), you can use that server to access, share, stream, and perform remote multi-device file management functions to any and all the storage on the server and all storage on the server’s network. You are virtualizing access to the server, any server attached storage such as a NAS, SAN, DAS, private cloud, and every PC and laptop on the same network as the server
Collaboration (FileFlex Enterprise only) - FileFlex Enterprise includes powerful content collaboration platform (CCP) capability that does not use the cloud and does not duplicate or sync your content to a third-party server. FileFlex Enterprise enables productivity and content collaboration for individuals and teams inside and outside the organization from source locations on your own storage, anytime, anywhere, on mobile or on your desktop, using your favorite applications like Office 365 or Google Docs. Activity tracking, audit trail, version control, file locking, a unified workflow across devices, and simple, secure access make your teams more productive and protects your information.
FileFlex is available for a 30 day free trial period with no credit card required. Outside of the trial, the purchase of a $34.95 annual subscription is required. The subscription is purchased in-app.
There is no cost for any non-subscriber contact to access and download files shared by a subscriber
Yes, the FileFlex web app works on all popular browsers, including Google Chrome, Microsoft Internet Explorer, Mozilla Firefox, Safari, Opera, etc. It also works on all popular mobile web browsers. A mobile app can be downloaded for Android from the Google Play store, and for iOS from the Apple App Store. The FileFlex web app can be accessed at https://share.fileflex.com.
Before installing the FileFlex app on your iOS device, you must first create a FileFlex account.
Step 1:
If you do not already have a FileFlex account, click here to create an account.
Step 2:
Once you have created a FileFlex account, click here to get the FileFlex iOS app.
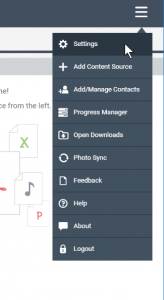
The free plan allows you to log on and remotely access anything that you have shared with others or anything that has been shared with you. You cannot, however, share or access anything else unless you upgrade to a paid plan. Upgrading is done inside the FileFlex app. To upgrade, open FileFlex, click the menu in the top right corner, then settings, then profile > billing status.
You can access your FileFlex account from any internet connected device via the FileFlex web app at https://share.fileflex.com. A mobile app can be downloaded for Android from the Google Play store and for iOS from the Apple App Store. You can also download the FileFlex desktop client at http://fileflex.com/installing-fileflex/.
Once your 30 day free trial has expired and you wish to subscribe to FileFlex, the purchase is done within app. Therefore, you will need to have a Credit card to pay for an Annual Subscription.
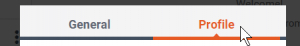
- There may be two reasons for why your FileFlex free trial may have endedafter 30 days even though you have an ASUSTOR NAS.1) To get the 1 year free trial, users must connect FileFlex to their ASUSTORNAS. If they create a FileFlex account, but do not connect it to theirASUSTOR NAS, they will only have a 30 day trial account, after which they'llneed to make an annual subscription. To connect FileFlex to theirASUSTOR, follow the instructions outlined in this link.2) Only the first user of the NAS to connect FileFlex to their ASUSTOR NASwill receive 1 year free. Subsequent users of the same NAS will receive a 30day free trial and can purchase FileFlex at a promotional price. To receivethe special price, they must have connected FileFlex to an ASUSTOR.To purchase, the user must open FileFlex and then select Settings fromthe main menu. In the Settings dialog box, they must open the Profile Taband then follow the instructions to purchase. Look in the FAQs section formore support on how to purchase FileFlex.If users have not connected FileFlex to their ASUSTOR, they will becharged the regular price of $34.95 for an annual subscription. However, ifusers have connected, they will receive the promotional price specific toASUSTOR users.
The annual subscription charges per user, and not per device. Once a user has subscribed to FileFlex, their FileFlex account allows the user unlimited devices (tablets, phones and computers) to connect to unlimited number of storage repositories.
Users can just add their devices (be it laptops, PC, phones or NAS) using "Add Content Sources" option from the open menu on the Global Application Bar. You would also want to download the FileFlex app on your cell phones.
Check https://help.fileflex.com/en/connecting-to-your-content to see how to add content sources to your FileFlex account.
Remote Access & Share Across Any Multi-Domain Hybrid-IT Infrastructure
Remote Access and Share Hybrid-IT On-Premises Storage
FileFlex Enterprise provides remote access and sharing to on-premises storage on servers, server-attached, network-attached, FTP and PC storage, cloud-hosted/multi-cloud IaaS storage such as MS Azure, Amazon S3, and Google Cloud, public and private cloud storage, and both self-hosted and MS hosted implementations of SharePoint.
FileFlex currently supports NAS devices from ASUSTOR, Synology, QNAP, Drobo, Western Digital and NETGEAR.
FileFlex currently supports Dropbox, Google Drive, OneDrive, Box, Amazon S3, Generic Amazon S3, Google Cloud and Azure.
If you want to access the storage on your computer remotely, then that computer must be on, connected to the internet, and not sleeping.
Other devices such as NAS (Network Attached Storage), servers, or server attached storage by nature are normally always on, connected to the internet, and not sleeping, and as such are always remotely accessible via FileFlex.
If you own a NAS, you can virtualize it with FileFlex. When you virtualize your NAS, you abstract the files stored on it from their physical location. Instead of accessing files stored on the NAS only through the network, when you virtualize it you can access, share, or stream your files from any computer, any laptop, any tablet, or any smart phone, from anywhere. You don’t have to upload or sync to third parties. Your data stays on your storage, on your premises, behind your firewall and under your control.
FileFlex virtualizes your NAS so that you can access, share, and stream your files from any device from anywhere. You can also let your family, friends, or any email contact, by permission, access or stream your stuff. In fact, when you install FileFlex on your NAS, it becomes a gateway to all the devices and storage attached to your network. FileFlex doesn’t just stop there. You can also use it to virtualize your PC, FTP, and server. Finally, you can link to your cloud providers so that all of your storage is at your fingertips through one dashboard.
Files for remote access can be stored on corporate servers, server attached storage – Direct Attached Storage (DAS), Storage Area Network (SAN), and Network Attached Storage (NAS) – FTP, PCs, laptops, public cloud services such as Dropbox, Box, Google Drive, and OneDrive, private clouds, and virtual private clouds.
Today we share files by sending them via email, copying them to a USB stick, or uploading them to a public cloud site – each with limitations and compromises. You cannot share large files via email, you must physically transport a USB stick, and public clouds have storage limits, making you pick and choose what to store and share.
FileFlex uses patented file virtualization technology which allows you to share files and folders from their source locations. There are no size or storage limits: you can share any type of file at its original quality, files can be kept on-premise behind your own firewalls, there are no uploads or copies to any third parties, and you do not have to choose what to sync and what not to sync.
Secondly, streaming and sharing is by permission only and is not a link that can be broadcast or tweeted by someone else to the whole internet. The recipient must be an email contact of yours. You control who can access your stuff. Finally, instead of disabling a link and affecting everyone who has that link, you can remove permissions person-by-person at any time if you want to stop sharing.
FileFlex provides better file sharing because FileFlex uses file access virtualization technology to allow file sharing from source locations. You do not upload the file to a secondary location, send a link, or attach a copy – you access the file where it rests in its source location. That means there are no storage limitations, no file size limits, no quality degradation (no compression), and no complicated IT type setup for the sharing of files.
Your files are stored on multiple devices and over multiple locations. FileFlex virtualizes access to those files, allowing you to remotely access and share them much like the way a debit card virtualizes money. Access to your files is abstracted from physical access to the storage location of those files. By connecting with all of your storage locations, you’ll have access to all of your files from one place. Your files do not get moved or uploaded to a third party, but stay where they are stored with encrypted access and sharing from their source locations. You can share with anyone who has an email address – they do not have to be set up by IT with device credentials. Your recipients only have direct access to the shared files and folders and do not even know where or on what device the shared files and folders are stored.
FileFlex lets you share any file or folder you've connected to your FileFlex account. For example, you can stream and share music, videos, and movies with your contacts.
You can share with anyone who has an email address. You simply need to add them to your contact list.
A virtual data room in FileFlex Enterprise is a folder located somewhere on your storage infrastructure that you share with someone and allow them upload rights.
A paid subscriber to FileFlex Enterprise can create as many virtual data rooms as they like without any additional incremental cost. They can share them with as many recipients as they like without cost to the recipient.
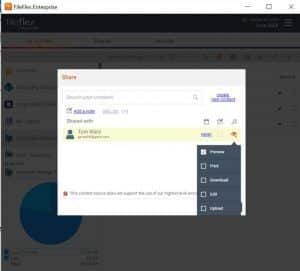
A user can make the data room ‘view-only’, they can allow for the recipient to make a hard copy with ‘Print’, can give them download rights or can give them editing rights at the user's discretion. Permissions can be set on a user-by-user basis with different users of the data room having different permission levels.
FileFlex Enterprise allows paid users to set up virtual data rooms that can be shared without cost to as many recipients as desired. A data room is a folder located somewhere on the storage infrastructure that the user shares with someone and allows them upload rights. The recipient has visibility to what is in the folder and they can add files to the folder by dragging and dropping them. Paid users can have as many virtual data rooms as they like - one for each client if they wish.
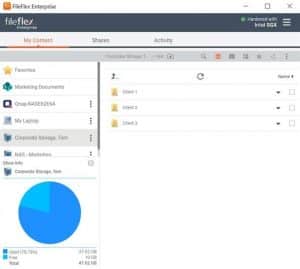
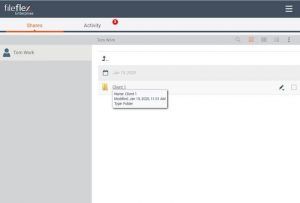
In the example below we have set up virtual data room folders for 3 clients by simply creating folders that can be shared.
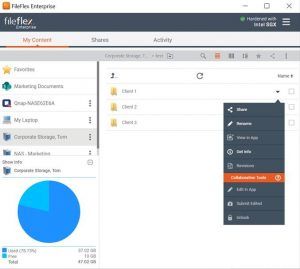
We then click the down arrow for the folder/data room that we want to share and choose ‘Share’.
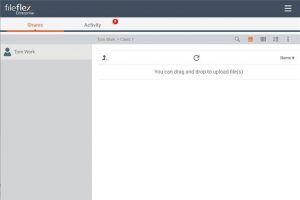
In the sharing options, we allow for uploads by clicking the ‘Upload’ radio button.
We can make the data room ‘view-only’, we can allow for the client to make a hard copy with ‘Print’, we can give them download rights or we can give them editing rights at our discretion. This can be set on a user-by-user basis with different users of the data room having different permission levels.
The recipient receives access to the folder.
They open the folder and then can drag and drop files into it.
The ability to create Virtual Data Rooms is a feature of FileFlex Enterprise. It is not available on the SMB/SOHO version.
In short, yes – FileFlex is arguably the world’s best file manager app for remote file management between multiple devices. Normally, if you want to create a folder, rename a file, or cut, copy, and paste for example, your file manager will only you perform file management functions to storage that is either on your device or networked to your device. It works for devices you are connected to, but not when you are remote. However, in today’s age, the traditional file manager app has simply not kept up with the demands of users that work remotely using multiple devices from anywhere in the world. This is where the powerful file access virtualization technology of FileFlex kicks in. FileFlex allows for file management across all your storage – not just the storage on your device or networked to your device. You can be remote.
FileFlex virtualizes access to your files and folders no matter where they are on your storage infrastructure. They could be on your local drive or they could be on a network drive, they could be on the server of a remote office or they could be on your corporate cloud. It doesn’t matter. With FileFlex, you can access your stuff no matter where it is stored. Not just access, but you can manage all your files and folders remotely no matter where they are stored. That means that even when you are working remotely, you can navigate and organize. You can cut, copy, paste, upload, move, delete, and rename your stuff from a smart phone, tablet or secondary computer, even when you are away. You don’t have to be in the office to organize your network drives; you can keep things organized from anywhere.
FileFlex doesn’t stop there. It turns networked devices into a powerful gateway into all storage. For example, with FileFlex on a server (or NAS, router or networked PC), you can use that server to access, share, stream and perform remote multi-device file management functions to any and all the storage on the server and all storage on the server’s network. You are virtualizing access to the server, any server attached storage such as a NAS, SAN, DAS, private cloud and every PC and laptop on the same network as the server.
FileFlex organizes all your storage from a single dashboard and all of your storage is displayed with the same hierarchical navigational file manager no matter what device your files are stored on. It allows you to remotely manage files on and between any of your storage drives.
FileFlex virtualizes access to your files and folders no matter where they are on your storage infrastructure. That means you can manage all your files and folders between storage devices – even if you are remote and even if they are not on the same network. FileFlex provides functions to cut, copy, paste, rename, delete, and move files, as well as upload and download files to any of the content sources you've added.
The file access virtualization technology of FileFlex allows you to manage all your files and folders remotely no matter where they are stored. That means that even when you are working remotely, you can navigate and organize. You can cut, copy, paste, upload, move, delete and rename your stuff from a smart phone, tablet, or secondary computer even when you are away. You don’t have to be in the office or on the network to organize your network drives; you can keep things organized from anywhere.
The traditional file manager app allows you to navigate and organize files on a local drive and mapped networked drives. It includes the ability to create folders, as well as cut, copy, paste, move, upload, and delete files. But that is where a traditional file manager app ends. It works for devices you are connected to, but doesn't connect you to your other storage.
FileFlex virtualizes access to your files and folders no matter where they are on your storage infrastructure. They could be on your local drive, or they could be on a network drive; they could be on the server of a remote office, or they could be on your corporate cloud. It doesn’t matter. With FileFlex, you can access your stuff no matter where it is stored. Not just access, but you can manage all your files and folders remotely no matter where they are stored. That means that even when you are working remotely, you can navigate and organize your files and folders. You can cut, copy, paste, upload, move, delete, and rename your stuff from a smart phone, tablet or secondary computer even when you are away. You don’t have to be in the office to organize your network drives; you can keep things organized from anywhere.
FileFlex doesn’t stop there. It turns networked devices into a powerful gateway into all storage. For example, with FileFlex on a server (or NAS, router, or networked PC), you can use that server to access, share, stream and perform remote multi-device file management functions to any and all the storage on the server and all storage on the server’s network. You are virtualizing access to the server, any server attached storage such as a NAS, SAN, DAS, private cloud, and every PC and laptop on the same network as the server.
FileFlex organizes all your storage from a single dashboard, and all of your storage is displayed with the same hierarchical navigational file manager no matter what device your files are stored on. It allows you to remotely manage files on and between any of your storage drives.
FileFlex has a layered approach to the security of your files. First, files stay in their source locations, and nothing is moved or copied to a third party. This means that it stays under your control, or in the case of corporate clients, under the umbrella of the corporate-owned infrastructure, behind the corporate firewall and under the control of IT. Privacy and security of information can be contained completely on-premise without worrying about breaches, outages, ownership, or who has access to data when it is stored and maintained by third parties. Second, users have high level encrypted direct access to the files with trusted certificates. This is the same level of protection offered by financial institutions to protect transactions over the internet. And third, FileFlex provides a log of data-in-motion activities (even for in-app activities via public clouds) for audit and regulatory compliance issues.
Real-time event logging provides an audit trail of file access actions – even if files are allowed and moved to a public cloud. This is particularly important for organizations that have to meet industry or governmental regulatory and compliance requirements.
Remotely accessing, sharing, and streaming media with FileFlex is private. FileFlex has a layered approach to the security of your files. First, files stay in their source locations, and nothing is moved or copied to a third party. Privacy and security of information can be contained completely on your own storage without worrying about breaches, outages, ownership or who has access to data when it is stored and maintained by third parties. Secondly, streaming and sharing is by permission only and is not link-based. You control who can access your stuff. And thirdly, users have high level encrypted direct access to the files with trusted certificates. This is the same level of protection offered by financial institutions to protect transactions over the internet.
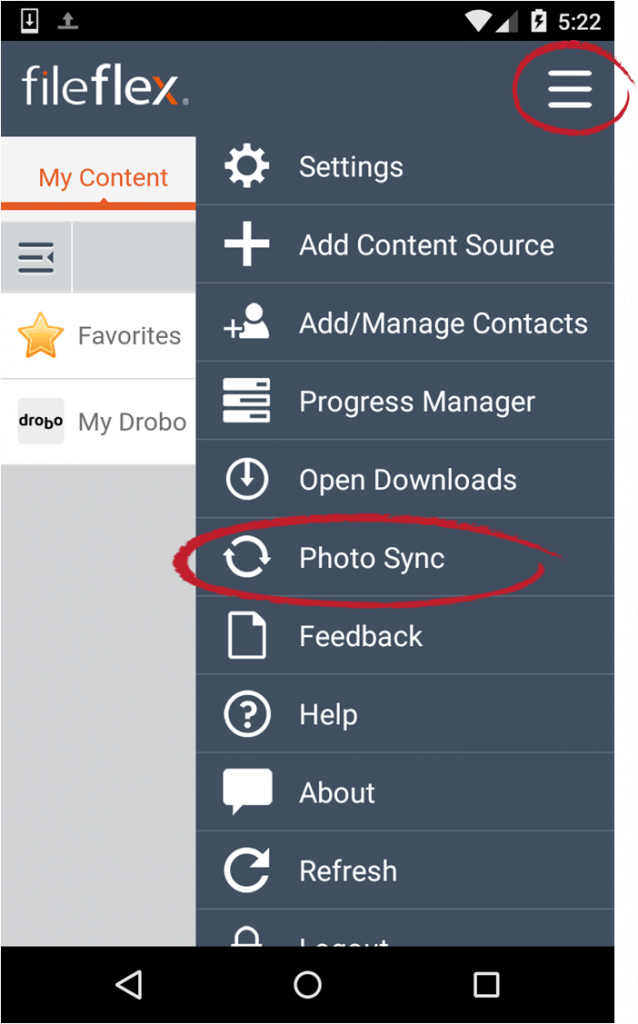
FileFlex includes the ability to automatically backup your photos and videos from your smart phones and tablets to your storage called Photo Sync. To use the Photo Sync feature, open FileFlex on the smart phone or tablet that you want to backup, then from the main menu in the top right corner (3 horizontal lines) select Photo Sync and then follow the wizard.
You can back up as many smart phones and tablets as you want.
You can store your backed up photos and videos to any storage repository you have added to FileFlex.
Yes - when you set up the Photo Sync feature, you can set up the option to only backup when the phone or tablet is connected to the Internet via WiFi so as to not consume your cellular data.
Photo Sync will only backup when you are connected to the Internet and your storage destination is turned on. If you are off-line when you take a photo or video, then FileFlex will wait until you are connected to the Internet and then backup your photos and videos. If you choose to backup by WiFi only, then it will wait until you are connected to the Internet via WiFi.
If your storage destination is not turned on - for example if you are backing up to a PC - then
FileFlex will wait until the destination is turned on and then backup your photos and videos.Otherwise FileFlex will immediately automatically backup your photos and videos as soon as you take them when you are connected to the Internet and your storage destination is ready to receive them.
FileFlex will backup to the storage destination you have specified and is only restricted by the amount of space available. For example, if you are backing up to a 500 GB drive and it has 300 GB available, you can backup up to 300 GBs of photos and videos.