What is Zero Trust Data Access (ZTDA)?
Top 7 Advantages of an Overlay Service
Overlay services revolutionize modern IT by providing a flexible, scalable, and cost-efficient virtual layer that enhances functionality, ensures seamless integration, and empowers […]
8 Benefits of Zero Trust Activity Monitoring
Zero Trust User Access Management: 4 Best Practices
Zero Trust Data Access for DIB Cybersecurity Strategy
How Zero Trust Data Access Can Facilitate Secure and Controlled On-Premises Network Access of Files and Folders
Critical Infrastructure Onboarding and Ease of Use Over Remote Access and Sharing Using Zero Trust Architecture
Critical infrastructure ease of use over remote access and sharing due to the complexity of the storage structure of modern organizations is […]
Critical Infrastructure Management Over Remote Access and Sharing Using Zero Trust Architecture
Critical infrastructure management and control over the remote access and sharing of unstructured data is achieved via a zero trust data access […]
Critical Infrastructure Regulatory Compliance via Zero Trust Architectures
Critical infrastructure regulatory compliance in regard to protecting remote access to unstructured data can be greatly enhanced through the use of zero […]
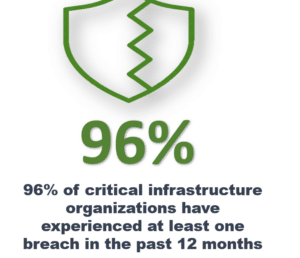
Protecting Critical Infrastructure Using Zero Trust Data Access – The Top 8 List
Protecting critical infrastructure can face unique challenges in regard to securing remote file access and sharing. With the need to protect sensitive […]