THE PLATFORM:
Get Data Layer Zero Trust Access to All of Your Storage Repositories
A data-layer Zero Trust Data Access (ZTDA) platform built to enforce per-request, least-privilege access, immutable auditing and seamless enterprise integrations – without migrating or copying your files.
Quick values: Per Request Authorization – Dark Storage Model – SIEM Export – Reversible Overlay
Executive Summary for IT
-
- Security: Object-level least privilege, short-lived tokens, immediate revocation.
- Operations: Non-invasive overlay deployment, centralized policy governance.
- Business: Reduces ransomware risk and preserves user productivity.
Architecture Overview – Policy Mediated, Dark Storage Model
The FileFlex Enterprise architecture ensures users never obtain direct, unauthenticated access to storage. All file operations are brokered by the FileFlex Enterprise policy layer and enforced via connectors – keeping storage “dark” unless explicitly authorized.
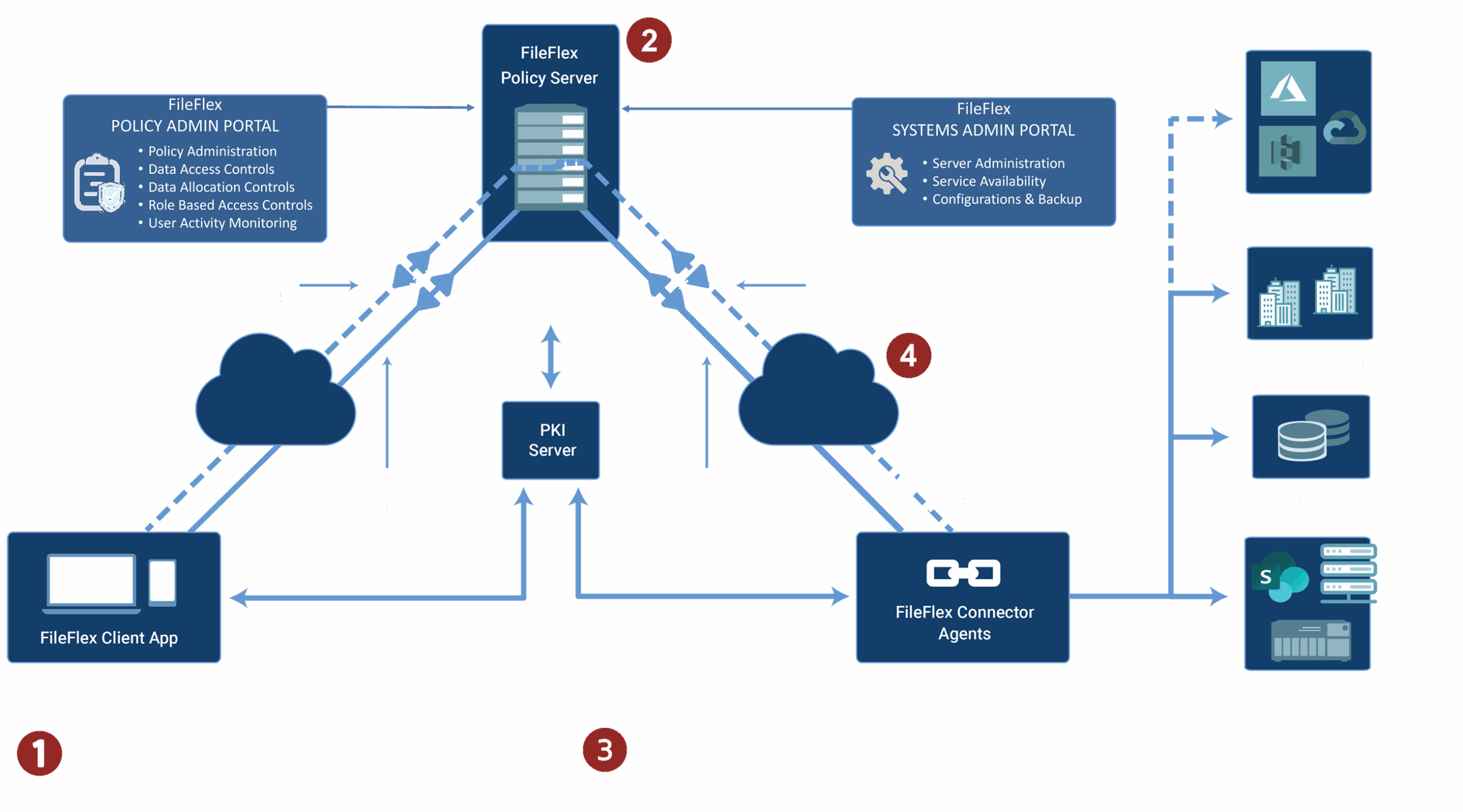

No Copying or Syncing of Data. Allows No Direct Access to Infrastructure.
See Top 10 Benefits of Restricting Direct Access to the Storage Infrastructure

Granular File and Folder Micro Segmentation

Least Privilege Access
See 9 Top Reasons Why Your Organization Needs Zero Trust Least Privilege Access

Centralized Control with Decentralized Administration
See Distributed Administration of Remote Unstructured Data Access for the Complex Supply Chain

IT Controlled Chain-of-Command
See Embracing Zero Trust Data Access for IT-Controlled Chain-of-Command
Zero Trust Enforcement – Per Request & Least Privilege
FileFlex Enterprise evaluates every file operation in real time. Policies support RBAC, ABAC, device enforcement, and storage-specific rules. Outcomes include: allow (read/write), read-only, block download, disable share, deny, and watermark.

Ephemeral, policy-bound access
Session Controls
Every access request is governed by short-lived, policy-bound sessions. Sessions are continuously enforced and automatically terminated, reducing exposure and preventing persistent access.

Least-privilege data visibility
Object-Level Policies
Access is enforced at the file and folder level. Users can only see and interact with the specific data they are authorized to access — with granular controls such as view-only, no download, and no sharing.

Audit-ready, SIEM-integrated
Immutable Logging
All file access and actions are immutably logged. Detailed activity records support audits, investigations, and real-time export to SIEM platforms for security monitoring.

Cybercrime is no longer a perimeter problem—it’s a data problem.
In this Q&A, cybersecurity veteran Ed Dubrovsky explains why data exfiltration has become the defining threat of the AI era, how attackers now operate at zettabyte scale, and why controlling access to unstructured data is critical to shifting the economics of modern cybercrime.
Federated Hybrid Access to Unstructured Data
Secure, Policy-Driven Access to On-Premises, SharePoint and Cloud Storage — Without Migration, Duplication, or Expanding Attack Surface.
Access all your on-prem and cloud storage through a single Zero Trust policy layer — no migration, no duplication, no direct user access.
Users see only what they’re allowed to see, with permissions enforced per repository (view-only, no download, no sharing). All actions are logged centrally and can be exported to your SIEM for complete auditability.
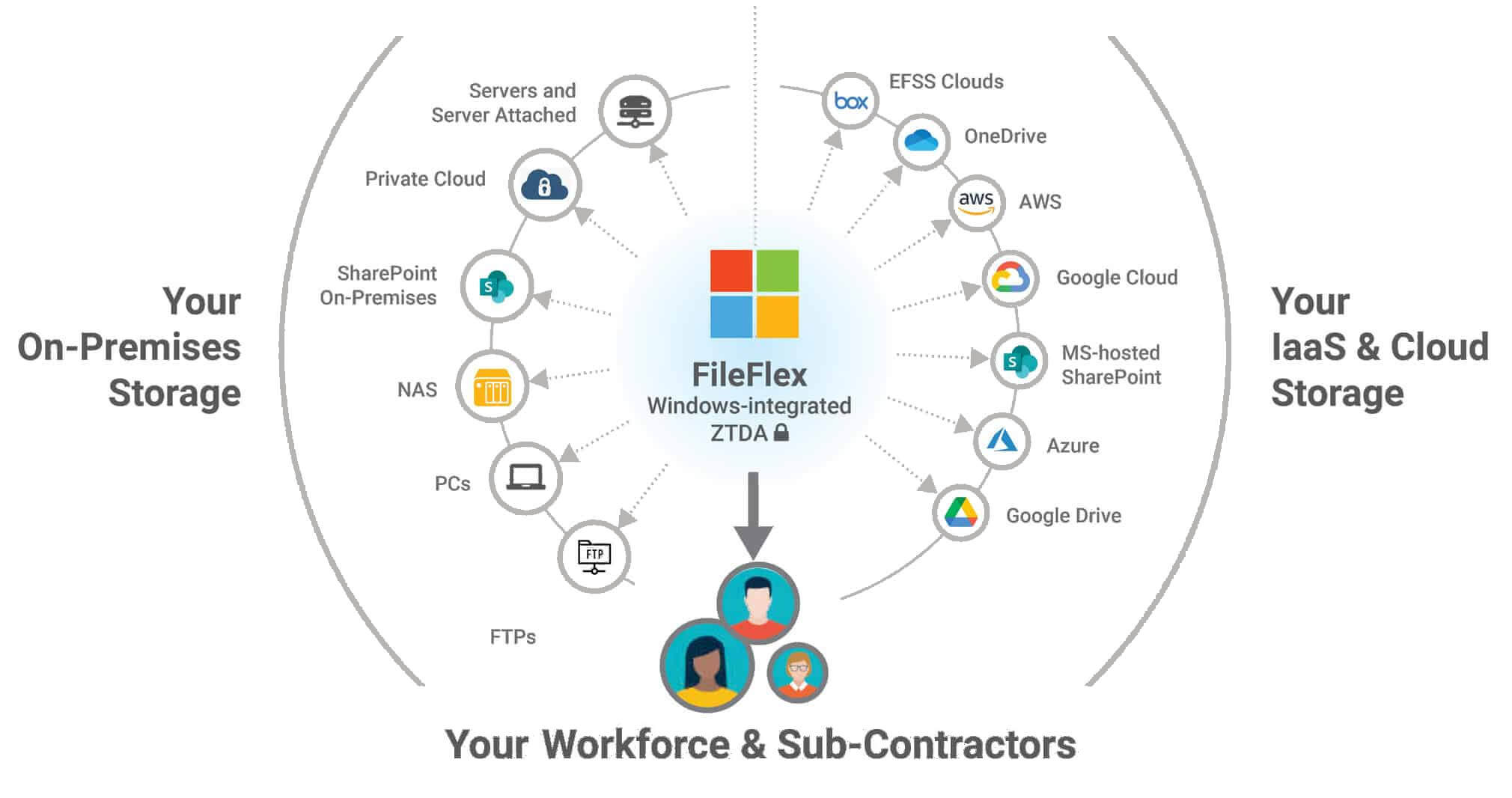
Federated Hybrid Access — One policy layer, many storage environments
Key Capabilities
-
Single policy plane across hybrid storage
Enforce consistent access rules across on-prem, private cloud, and public cloud repositories. -
No data migration or synchronization
Files remain in their original locations; FileFlex federates access rather than copying data. -
Dark storage by design
Storage repositories are never directly exposed to users or endpoints. -
Least-privilege, per-repository access
Permissions can be set per user, per storage source (view-only, no download, no sharing, etc.). -
Unified auditing across environments
All access events are logged centrally and can be exported to SIEM platforms.
Federated Hybrid Access reduces operational complexity, eliminates inconsistent access models, and closes the security gaps introduced by VPNs, file sync tools, and unmanaged cloud sharing — all without re-architecting existing storage.
Administration & Operational Controls
Comprehensive Admin Surface for IT: Identity Integration, Policy Authoring, Storage Management, Delegated Admin, and Audit Search
Centralized Control. Decentralized Enforcement.
The management console allows IT administrators to provide subsidiaries, partners and supply chains to add their own storage repositories and users to FileFlex Enterprise as siloed tenants while the centralized IT administrator maintains control, visibility and access over all tenants.
See Distributed Administration of Data Access for the Complex Supply Chain

Strong User Management
Set user permissions and control access to the storage and files they can access. Entra ID / Azure AD, Active Directory sync, SAML, Okta integrations
Read Why Zero Trust Data Access User Management is Crucial for IT

Robust Storage & Sharing Management
Granular control over sharing and storage permissions micro-segmented down to file level to protect PHI, PII and confidential data.
See Top 8 Reasons for Zero Trust Storage Management and Top 6 Reasons You Need Zero Trust File Sharing Management.
Comprehensive Data Activity Tracking
With an immutable event store, FileFlex logs all activities across your enterprise storage and sends log data to your SIEM software, where you can create relevant rules and alerts. It provides unlimited visibility to all remote data access and shares with a searchable audit console.
Read Top 8 Reasons Your Organization Needs Zero Trust Data Activity Tracking
Data Workflow Transformation Deep Dives
Zero Trust File Sharing
Policy-driven sharing with no data movement, granular permissions, and full auditability — enforced per request.
See Top 13 Reasons to Use a Zero Trust Secure File-Sharing Platform.
VPN Replacement
Replace broad network access with per-request data access to reduce lateral movement risk.
See 19 Advantages of the Zero Trust Data Access VPN Alternative.
Virtual Data Rooms
Create project-based VDRs with strict RBAC, timed access, and watermarking for M&A, legal, and accounting operations.
Read Top 13 Reasons to Adopt Zero Trust Secure Virtual Data Rooms.
Large File Collaboration
Stream and partial access patterns for CAD and media workflows to avoid sync and copy overhead.
See 16 Top Reasons to Adopt a Content Collaboration Platform Built on a Zero Trust Architecture
Zero Trust Managed File Transfer (MFT)
Replace staged file transfers with policy-enforced access to data in place. Eliminate temporary files, reduce attack surface, and maintain complete auditability.
See 19 Reasons Why Organizations Need Zero Trust Data Access as a Managed File Transfer Alternative.
Secure FTP Replacement
Retire legacy FTP by placing file servers behind a Zero Trust policy layer. Remove open ports and shared credentials while enforcing least-privilege access and full visibility.
Read 24 Reasons to Use Zero Trust Data Access as an FTP Alternative.
SharePoint / M365 Enhancement
Apply data-layer policies to SharePoint repositories; enforce view-only, watermarking, and restrict downloads.
Read 19 Reasons Why Zero Trust Data Access is an Essential SharePoint Add-in.
Outlook and Secure Attachments
Share attachments with policy-controlled links with revoke capability and audit trails.
See 21 Reasons to Supplement Microsoft 365 E5 Security with Zero Trust Data Access.
Ransomware Mitigation
Reduce Attack Surface, Stop Lateral Movement, Detect Exfiltration, Accelerate Response
Detect Ransomware Attacks in Process
FileFlex reduces ransomware risk by enforcing least-privilege access to unstructured data and limiting lateral movement. Unusual data access or extraction patterns can be detected and alerted on early — helping identify ransomware activity during the exfiltration phase, before encryption occurs.
- Early Detection of Exfiltration — activity analytics and SIEM export spotlight unusual data extraction.
- Least-privilege enforcement — policies ensure users only get the access they need.
- Dark Storage prevents direct exposure of SMB/NFS mounts.
- Per-object Authorization prevents blanket access that lets attackers pivot.
- Short-Lived Tokens reduce token misuse
- Revocation in seconds to limit ongoing compromise.
- Limited Lateral Movement — compartmentalized access reduces spread of malware.
- Immutable Audit Trails — every action logged for compliance and forensic readiness.
Read How to Reduce Ransomware Risk Using Zero Trust Data Access (ZTDA)
Technology Alliance Partners

Integration Technology Partners

Built for Regulatory Compliance
Enforce Least-Privilege Access, Auditability, and Data Governance Across Unstructured Data to Support Regulatory and Compliance Requirements.

GDPR
FileFlex Enterprise provides secure file access, sharing and collaboration which supports and augments an organization’s GDPR compliance endeavors… More

HIPAA
FileFlex Enterprise is the ideal file
sharing and collaboration tool for HIPAA Covered Entities and HIPAA Business Associates… More

NIST
FileFlex Enterprise supports the published best “Access Control” practices for data access outlined in NIST SP-800-171v2… More

CMMC
FileFlex Enterprise supports the published best “Access Control” practices for data access outlined in the Department of Defense’s Cybersecurity Maturity Model Certification… More

FFIEC
FFIEC guidelines require financial institutions to implement robust cybersecurity frameworks such as Zero Trust Data Access More

Aids FedRAMP
FedRAMP Compliance is enhanced with Zero Trust Data Access for secure remote access and sharing of unstructured data stored in FedRAMP-authorized data centers. More

GLBA
GLBA compliance is strengthened through Zero Trust Data Access, which enhances data security, minimizes insider threats, and ensures the auditing of sensitive information in financial institutions. More

DORA
DORA compliance for file sharing, access and collaboration necessitates the implementation of Zero Trust Data Access (ZTDA). More

Local Privacy Regulations
ZTDA aids local privacy regulation compliance in protecting personal data. More

Critical Infrastructure Regulatory Compliance
Critical infrastructure regulatory compliance in regard to protecting access to unstructured data can be greatly enhanced through the use of zero-trust architectures. More

CCPA/CPRA
California Privacy and Cybersecurity Standards necessitate the implementation of Zero Trust Data Access (ZTDA. More
DSPM Visibility. Zero Trust Enforcement.
DSPMs reveal where data is exposed. FileFlex enforces policy-driven access to reduce risk at the source.
See DSPMs and Zero Trust Data Access: A Powerful Duo for Zero Trust Data Security
Cloud-Like Access, On-Prem Control
Provide users with secure, cloud-style access to on-premises files. Full Zero Trust enforcement ensures data remains protected and auditable.
Read – Revitalizing On-Premises Storage with Zero Trust Data Access
Deployment & Rollback
Pilot with a small set of repositories or business units. FileFlex Enterprise deploys as an overlay, uninstalling removes no persistent changes from storage and preserves files.
Think Microsoft Has You Covered? Think Again.
Your Microsoft tools handle identity, but fall short on data-centric security. Learn why Zero Trust Data Access is the missing layer your Microsoft environment needs to protect unstructured data, reduce risk, and meet compliance head-on.
Read – Why Microsoft-Centric Security Isn’t Enough: The Case for Zero Trust Data Access

Reduces Your Costs
Zero Trust Data Access technology as implemented by FileFlex reduces your maintenance and support costs and VPN, FTP, MFT, file sharing, content collaboration, virtual data room and cloud storage use to dramatically reduce your costs.
Read How Zero Trust Data Access Cuts Costs in Organizational Operations.