File Sharing and Collaboration Evolution from First Generation Platforms to Zero Trust Data Access
File sharing and collaboration have significantly evolved over time, with first-generation platforms paving the way for innovative Zero Trust Data Access solutions […]
Higher Education Institutions Bolster Data Security with Zero Trust Data Access
Higher education institutions face increasing challenges in safeguarding sensitive student information, research data, and administrative records within the digital realm. To address […]
Data Governance, Cybersecurity and Zero Trust Data Access: The Essential Pillars to Protect Data Assets
Data governance, cybersecurity and zero trust data access are three essential pillars for organizations seeking to protect their valuable data assets in […]
The Top 7 Benefits of Network File Access Control Using Zero Trust Data Access
Network file access control using zero trust data access is crucial for safeguarding sensitive information contained within unstructured data. Intellectual property, financial […]
How to Reduce Ransomware Risk Using Zero Trust Data Access (ZTDA)
Ransomware attacks in 2023 pose a pervasive and costly threat to organizations, but adopting Zero Trust Data Access (ZTDA) through FileFlex Enterprise […]
How to Improve Network Security Using Zero Trust Data Access
Network Security is fortified through the implementation of Zero Trust Data Access, providing granular control, reduced attack surface, better regulatory compliance alignment, […]
How Zero Trust Data Access Can Facilitate Secure and Controlled On-Premises Network Access of Files and Folders
Why Your Zero Trust Security Model Must Include Zero Trust Data Access (ZTDA)
Zero trust security model is a security approach that assumes that every user, whether inside or outside of the organization’s perimeter, is […]
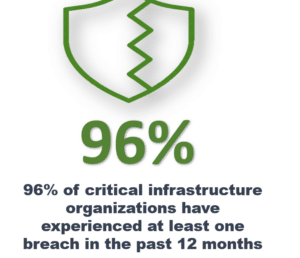
Critical Infrastructure Onboarding and Ease of Use Over Remote Access and Sharing Using Zero Trust Architecture
Critical infrastructure ease of use over remote access and sharing due to the complexity of the storage structure of modern organizations is […]
Critical Infrastructure Management Over Remote Access and Sharing Using Zero Trust Architecture
Critical infrastructure management and control over the remote access and sharing of unstructured data is achieved via a zero trust data access […]