
The UK has issued a legal demand for an iCloud backdoor under the Investigatory Powers Act, prompting Apple to withdraw Advanced Data Protection (end‑to‑end encryption) in the UK. On‑premises storage secured with Zero Trust Data Access (ZTDA) offers organizations control without trusting a backdoor—including FileFlex as a practical example.
UK iCloud Backdoor: Secure On‑Prem iCloud with ZTDA
Estimated reading time: 6 minutes
Table of Contents
-
-
-
- Introduction: How the UK’s ‘Snooper’s Charter’ Threatens Data Security and the Role of Zero Trust Data Access in Safeguarding Privacy
- UK Orders Apple to Create Global iCloud Backdoor
- What is the UK Investigatory Powers Act 2016 (“Snooper’s Charter”)?
- Impact of the UK Investigatory Powers Act on Other Cloud Providers
- Similar Investigatory Powers in Other Countries
- Preserving Privacy by Storing Data On-Premises
- Benefits of Pairing On-Premises Storage with Zero Trust Data Access of FileFlex Enterprise
- Conclusion: Securing Your Data in an Increasingly Vulnerable World with FileFlex Enterprise
-
-
Introduction: How the UK’s ‘Snooper’s Charter’ Threatens Data Security and the Role of Zero Trust Data Access in Safeguarding Privacy

What Is the “UK iCloud Backdoor?
The UK government issued a Technical Capability Notice under the Investigatory Powers Act, demanding Apple build a backdoor into its Advanced Data Protection (E2EE) iCloud service content. In response, Apple withdrew ADP from UK users and launched legal challenges, supported by WhatsApp and US authorities :contentReference.
What is the UK Investigatory Powers Act 2016 (“Snooper’s Charter”)?
On Friday, February 7, 2025 the Washington Post reported that the UK government has ordered Apple to create a backdoor granting access to iCloud accounts worldwide, not just in the UK. This demand is based on the Investigatory Powers Act of 2016, commonly known as the “Snooper’s Charter,” which allows authorities to compel companies to provide access to user data.
Apple has been asked to enable broad access to fully encrypted content stored in iCloud, meaning security agencies could view user data regardless of their location. This includes data protected by Apple’s Advanced Data Protection, which provides end-to-end encryption for iCloud backups, ensuring that even Apple cannot decrypt the information.
The Investigatory Powers Act (IPA) 2016, often called the “Snooper’s Charter,” is a UK law that grants broad surveillance powers to the government. It forces tech companies, ISPs, and telecom providers to store and provide access to user data upon request. It includes requirements for:
-
Data Retention
-
- Internet Service Providers (ISPs) must store users’ web browsing history (Internet Connection Records) for 12 months. UK authorities can access this data without a warrant in some cases.
-
Mass Surveillance & Bulk Data Collection
-
- The law allows government agencies (MI5, MI6, GCHQ, and law enforcement) bulk interception of emails, texts, calls, and metadata on both UK and foreign citizens and GCHQ (the UK’s intelligence agency) is given broad powers to hack into systems globally.
-
Tech Companies Must Comply with Decryption Requests
-
- Companies like Apple, Google, Microsoft, and others can be forced to remove encryption (if feasible). This is done via “technical capability notices” (TCNs), which force companies to build a backdoor or provide decryption keys. If a company receives a TCN, it cannot disclose it due to secrecy requirements.
-
“Equipment Interference” (Hacking Powers)
-
- UK agencies can hack into computers, networks, and devices (including foreign systems) and they can remotely install software to gather information.
-
International Impact (Global Reach)
-
- The IPA applies not just to UK-based companies but also to foreign companies operating in the UK. These companies must comply with UK surveillance demands even if the data is stored outside the UK. This is why Apple’s iCloud backdoor request affects users worldwide.
Impact of the UK Investigatory Powers Act on Other Cloud Providers
The UK government can demand access to encrypted data from cloud providers like Apple, Google, and Microsoft, without notifying users. Companies that refuse to comply risk heavy fines or being banned from operating in the UK. This has sparked controversy due to concerns over privacy violations, lack of oversight, and potential abuse—as mass surveillance powers could extend beyond national security to monitor journalists, activists, or political opponents. Additionally, forcing Apple to create a backdoor could itself create a vulnerability that can be exploited by hackers, criminal organizations, and foreign security agencies and it sets a global precedent, pressuring other tech firms to weaken encryption, ultimately undermining user privacy worldwide.
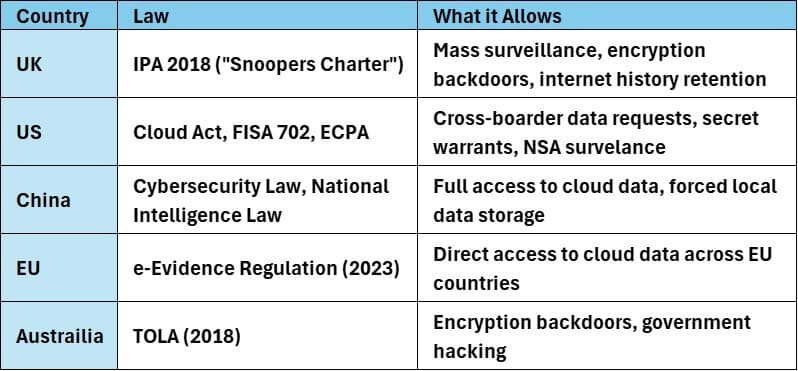
Similar Investigatory Powers in Other Countries
The U.S. and several other countries have legal mechanisms that allow authorities to secretly access cloud data. Here are some key laws and frameworks:
United States
- Cloud Act (2018) – The Clarifying Lawful Overseas Use of Data (CLOUD) Act allows U.S. law enforcement to compel cloud providers like Microsoft, Google, Apple, Dropbox, and Box to turn over user data, even if it’s stored in foreign countries. It also enables reciprocal agreements with other governments, allowing them to request data from U.S. companies.
- Electronic Communications Privacy Act (ECPA, 1986) – Under the Stored Communications Act (SCA), a section of ECPA, law enforcement can obtain user data from cloud providers with a warrant, and companies are often barred from notifying users.
- FISA Section 702 (Foreign Intelligence Surveillance Act, 2008) – Allows intelligence agencies (e.g., NSA, FBI) to collect and monitor data from cloud services without a warrant if the target is a non-U.S. citizen abroad.
- National Security Letters (NSLs) – The FBI can issue NSLs to obtain cloud data for national security investigations. These often come with indefinite gag orders, preventing companies from disclosing the request.
Other Countries with Similar Powers
- European Union: e-Evidence Regulation (2023, expected implementation in 2026) – Allows EU authorities to directly request cloud data from providers across member states.
- China: Cybersecurity Law (2017) & National Intelligence Law (2017) – Requires cloud providers to store Chinese users’ data locally and provide access to authorities.
- Australia: Telecommunications and Other Legislation Amendment (TOLA) Act (2018) – Allows authorities to require tech firms to build “capabilities” to access encrypted data.
- India: Information Technology Act (2000) & Intermediary Guidelines (2021) – Requires cloud providers to hand over user data upon government request.
Most of these laws include non-disclosure provisions, preventing companies from informing users when their data has been accessed. However, major cloud providers (Microsoft, Google, Apple) publish transparency reports listing the number of government requests received.
Preserving Privacy by Storing Data On-Premises
Storing sensitive data on-premises (i.e., within an organization’s own infrastructure, rather than in the cloud) can significantly strengthen privacy by offering more control over how the data is stored, accessed, and secured. Here’s how:
-
Complete Control Over Data Access
-
- Limit who can access data: By storing data locally, organizations can tightly control access, ensuring that only authorized personnel or systems can retrieve sensitive information.
- No third-party access: With on-premises storage, companies avoid giving external cloud providers access to the data, reducing the risk of potential data breaches or government access without proper oversight.
-
Customizable Security Measures
-
- Tailored security protocols: Organizations can implement and enforce custom encryption methods, firewall protections, and access controls based on their specific needs and security requirements.
- Data encryption at rest and in transit: Sensitive data can be encrypted on local servers, both when stored (at rest) and when being transmitted (in transit). This reduces the risk of unauthorized access.
-
Compliance with Regulations
-
- Meet regulatory requirements: Certain industries or countries may have strict data protection laws (e.g., GDPR, HIPAA) that mandate keeping data within specific regions or preventing third-party access. On-premises storage allows for full compliance with such regulations.
- Local control over compliance audits: Organizations can manage their own audits and ensure compliance with privacy laws, as they have direct oversight of how and where their data is stored.
-
Avoiding Shared Cloud Risks
-
- Isolation from multi-tenant cloud environments: In cloud storage systems, data is often shared across multiple customers (multi-tenancy), which can lead to potential vulnerabilities or accidental data leakage. On-premises storage ensures data isolation, which reduces these risks.
- Avoiding cloud provider backdoors or compromises: Cloud providers may be subject to government requests for data, or vulnerabilities in their infrastructure might be exploited. On-premises storage means that organizations are less likely to be exposed to these risks, especially when using advanced security measures.
-
Increased Visibility & Monitoring
-
- Enhanced monitoring: Storing data on-premises allows for continuous, real-time monitoring of the system’s security. Organizations can employ advanced threat detection and other proactive security measures to protect sensitive data.
- No external data access means it’s easier to monitor and log all access attempts to sensitive information, helping detect any unauthorized or suspicious activity early.
-
Data Ownership & Control
-
-
- Data sovereignty: By keeping data on-premises, organizations retain full ownership and control over their data, ensuring it is stored in compliance with their internal policies and the legal frameworks of their jurisdiction.
- Protection from external interference: Without relying on third-party cloud providers, there is less risk of foreign governments or other external entities accessing the data without the organization’s consent.
-
Benefits of Pairing On-Premises Storage with Zero Trust Data Access of FileFlex Enterprise
Combining on-premises storage with the Zero Trust Data Access of FileFlex Enterprise provides an optimal solution that combines the privacy and control of local storage with the security and flexibility of Zero Trust access controls. Here’s how this pairing offers distinct advantages:
-
Enhanced Security with Zero Trust Data Access
-
- No Implicit Trust: The Zero Trust model ensures that every access request is authenticated, authorized, and continuously verified, regardless of the user’s location or network.
- Granular Access Control: FileFlex Enterprise provides fine-grained control over who can access what data, ensuring only authorized users can access specific files or folders, even if they’re stored on-premises.
- Continuous Monitoring and Verification: Each access attempt is validated and tracked, ensuring that unauthorized users or compromised devices cannot gain access to sensitive data.
-
Privacy and Data Sovereignty
-
- Full Control of Data Location: Storing sensitive data on-premises ensures that the organization retains complete ownership and control over where and how data is stored, avoiding third-party access or the risk of remote data breaches.
- No Data Leaving the Premises (unless authorized): With Zero Trust, file access can be granted without moving or copying data to external locations, reducing the risk of exposure while still enabling secure collaboration.
- Privacy-Compliant: Organizations can maintain compliance with data sovereignty laws (e.g., GDPR) while using FileFlex Enterprise to enforce strict access controls over sensitive data stored locally.
-
Secure Remote Access
-
- Access from Any Device with Zero Trust Security: Users can securely access on-premises data remotely (such as from home, traveling, or client sites) without compromising security. FileFlex Enterprise enforces Zero Trust authentication for each device and session, ensuring only trusted users can access the data.
- Preventing Lateral Movement: Even if an attacker compromises one device or account, the Zero Trust approach ensures they cannot easily move laterally within the system to gain access to other files or data on the network.
-
Protection Against Insider Threats
-
- Restricted Access Based on Roles: FileFlex Enterprise allows organizations to enforce role-based access controls (RBAC), limiting access to data based on the user’s role, need-to-know basis, and trust level.
- Least Privilege Principle: Even if an internal user is compromised, they can only access the specific data they are authorized to view, minimizing the potential impact of insider threats.
-
Simplified User Authentication and Access Control
-
- Single Sign-On (SSO) and Multi-Factor Authentication (MFA): FileFlex Enterprise integrates SSO and MFA, ensuring that only authenticated users with the correct credentials can access on-premises data securely. This streamlines the user experience while maintaining strong security controls.
-
Seamless Sharing and Collaboration Without Compromising Security
-
- Secure Sharing Across Departments: On-premises data can be shared securely across departments or with external partners without the need to move it to the cloud, reducing exposure. FileFlex Enterprise’s Zero Trust model ensures secure collaboration while maintaining control over the data.
- No Need for External Storage Solutions: With Zero Trust access, organizations can collaborate without moving files to cloud environments, preserving privacy and eliminating the need for external cloud storage.
-
Scalability Without Compromising Control
-
- Flexibility to Scale: Combining on-premises storage with FileFlex Enterprise allows organizations to scale their storage needs locally, without losing security or control over the data.
- Hybrid Model: Organizations can integrate on-premises storage with cloud resources (if needed) while using Zero Trust Data Access to seamlessly secure access to all resources, ensuring data security without sacrificing flexibility in scaling.
-
Comprehensive Auditing and Compliance
-
- Continuous Audit Trails: Every access request is logged and can be reviewed for audit purposes. This is essential for industries with strict compliance requirements (e.g., healthcare, finance).
- Support for Compliance Frameworks: By combining on-premises storage with Zero Trust access, organizations can better adhere to data protection regulations such as GDPR, HIPAA, and others, ensuring that access controls, audits, and data storage practices meet compliance standards.
-
Reduced Risk of Data Breaches
-
- Zero Trust Minimizes Attack Surface: By continuously verifying every access request and enforcing strict policies, the risk of a data breach is significantly reduced. FileFlex Enterprise’s Zero Trust Data Access approach minimizes vulnerabilities caused by outdated security models like VPNs or firewalls.
-
Cost-Efficiency
-
- Optimize Existing Infrastructure: Leveraging existing on-premises storage for secure file access can save organizations the cost of moving data to cloud solutions, while still implementing robust Zero Trust security controls with FileFlex Enterprise.
- Lower Risk of Expensive Data Breaches: By reducing the likelihood of breaches with Zero Trust security, organizations avoid the costly consequences of a data breach, such as fines, loss of customer trust, and reputation damage.
| Characteristic | Apple iCloud (with UK Backdoor) | On‑Prem + ZTDA Alternative |
| Encryption Control | Weakened (no ADP for UK users) (virtru.com) | Full control via self-hosting |
| Regulatory Compliance | Subject to UK Investigatory Powers Acts | Governed by internal policies |
| Trust Model | Requires trusting Apple + government | Trust only yourself |
| Auditability | Logs accessible to legal requests | Full, private audit logs via ZTDA |
Conclusion: Securing Your Data in an Increasingly Vulnerable World with FileFlex Enterprise
The UK government’s demand for a backdoor into iCloud underscores the growing risks to data privacy, as governments worldwide push for more access to encrypted information. To protect sensitive data, organizations must take proactive steps, such as storing data on-premises to maintain control and reduce exposure to external threats. By combining on-premises storage with the Zero Trust Data Access of FileFlex Enterprise, companies can further enhance security by enforcing strict access controls, ensuring that only authorized users can access critical data, and preventing unauthorized surveillance or breaches. This combination provides secure remote access, protects against insider threats, and offers comprehensive monitoring, auditing, and compliance features, ensuring both privacy and adherence to regulatory requirements. As the global conversation on data security intensifies, pairing on-premises storage with FileFlex Enterprise offers a future-proof solution to safeguard data and maintain control, free from government overreach and external vulnerabilities.
See also Revitalizing On-Premises Storage with Zero Trust Data Access, and Why a Zero Trust Data Access Decentralized Data Platform is Strategically Superior to Centralized Cloud File Access, Sharing and Collaboration.
Learn More About FileFlex Sign Up for a Free TrialFrequently Asked Questions
What was the UK’s iCloud backdoor demand?
The UK’s Investigatory Powers Act allowed it to compel Apple to provide access to encrypted iCloud data—called a Technical Capability Notice. In response, Apple withdrew its Advanced Data Protection feature in the UK and filed a legal challenge.
Why did Apple remove Advanced Data Protection in the UK?
Apple pulled ADP in the UK because the government’s backdoor demand would weaken end-to-end encryption. Apple chose removal over compromising user privacy.
What is the best alternative to iCloud with a UK backdoor?
On-premises storage secured with Zero Trust Data Access (ZTDA) eliminates backdoor risk—giving complete authority over encryption and access. FileFlex is an example platform enabling this approach.